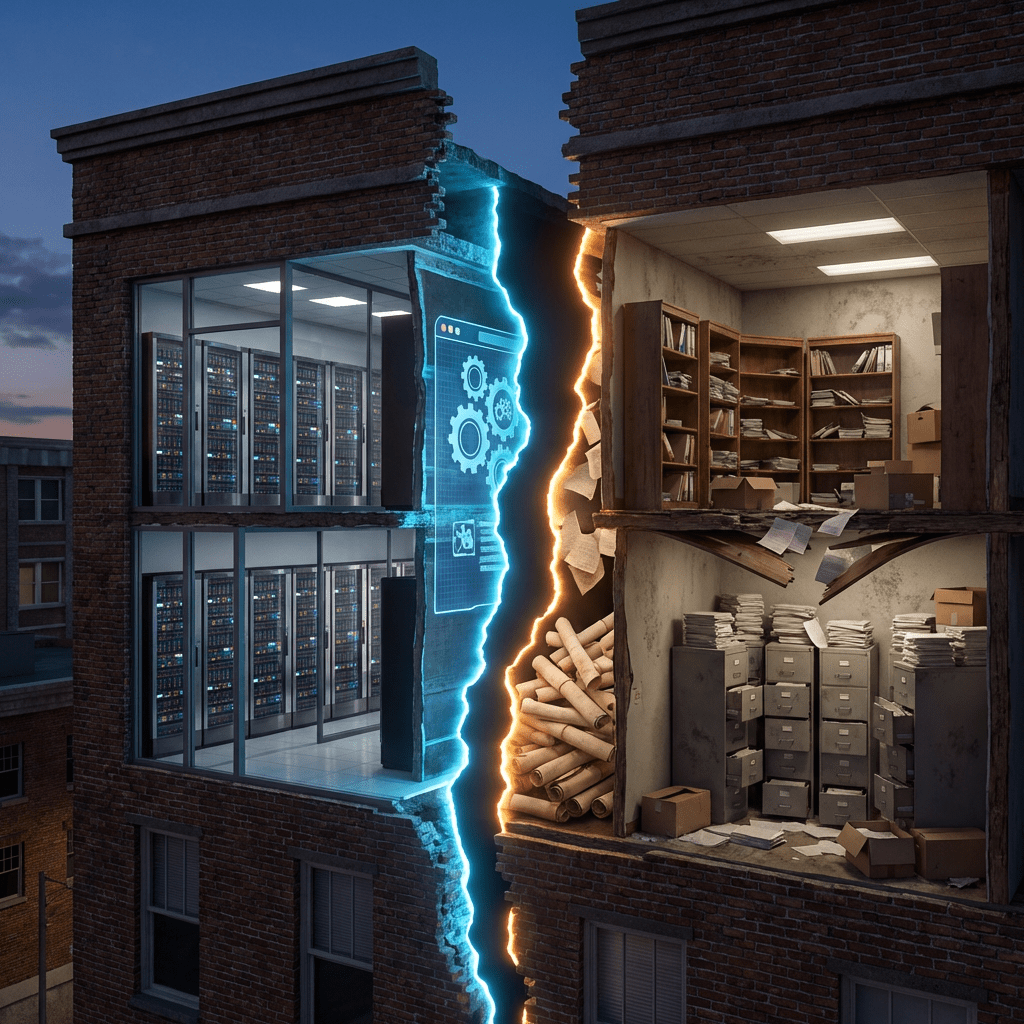
Most security programs are built by people who understand threats. Few are built by people who also understand liability. That gap is where programs break.
The Gap Nobody Talks About
Security programs fail in predictable ways, misconfigured infrastructure, alert fatigue, underfunded tooling. These are engineering problems, and most CISOs handle them well enough.
The failures that don’t make post-mortems look different. A breach notification goes out four days late because nobody pinned down what “discovery” meant under state law. IR logs get turned over in discovery because outside counsel didn’t know they existed. A vendor contract indemnifies the wrong party because the security team signed off on language they couldn’t parse.
Those aren’t IT failures. They’re governance failures with legal consequences, and they rarely surface until the damage is done.
Breach notification, the 72-hour problem
GDPR Article 33 gives you 72 hours from the moment you become “aware” of a breach to notify the relevant supervisory authority. The CCPA has its own clock. State laws have their own triggers. None of them agree on what “aware” means.
This produces a common failure: IR teams log events, escalate through triage, and spend days confirming scope before anyone asks whether the notification window is already running. By the time legal gets looped in, you’re late.
Notification timelines belong in the IR runbook, not in a separate legal policy document that nobody opens during an incident. The moment a P1 is declared, the clock should be visible in the incident channel. Awareness triggers legal obligation. Awareness does not require certainty about scope.
“Aware” is a term of art. It doesn’t mean “confirmed.” That distinction is the difference between compliant and exposed.
Evidentiary chain of custody in incident response
Most IR teams capture logs, preserve disk images, and document findings, good forensics practice. Far fewer treat those artifacts as potential evidence subject to chain of custody requirements.
That distinction matters when an incident becomes litigation, a regulatory investigation, or an insurance claim. Log files copied without hash verification. Memory dumps on a shared drive with write access. Analyst notes that mix observation with speculation. These start as defensible technical artifacts and become legal liabilities the moment someone subpoenas them.
IR teams work to understand what happened. Litigation demands something different: authenticated, unmodified artifacts with documented custody, because the objective shifts from understanding to proving. Standard IR practice doesn’t meet evidentiary standards by default. That gap requires deliberate process design built into the IR workflow before an incident occurs, not after.
Legal training doesn’t make someone a forensic examiner or a lawyer. It forces the right questions before an investigation goes sideways in court.
Vendor contracts and security obligations
Third-party risk programs are standard. Most organizations have questionnaire workflows, risk tiers, and periodic reviews. Almost none of that effort produces enforceable contractual obligations unless someone reads the contracts.
Standard SaaS agreements routinely cap vendor liability at fees paid in the prior 12 months, exclude consequential damages, and define “reasonable security” by reference to the vendor’s own policies. Security teams sign off on vendor onboarding without reading the MSA.
Understanding indemnification clauses, limitation of liability provisions, and how breach notification obligations flow through a contract changes what you push for in negotiations. “Unlimited liability for data breaches” won’t fly with most vendors. But “notification within 24 hours of a confirmed incident affecting customer data” is negotiable, if you know to ask for it in writing.
Security questionnaire results and vendor risk scores don’t create legal obligations. The contract does. If your vendor risk program doesn’t connect to contract language, it’s compliance theater.
Regulatory frameworks as architecture inputs
Most security teams treat NIST, ISO 27001, and SOC 2 as checklists. Map controls, generate evidence, pass audits. That’s compliance. It’s not the same as building a program that reflects the actual regulatory environment the organization operates in.
HIPAA’s Security Rule distinguishes “required” from “addressable” controls, a distinction that changes how you document implementation decisions. FTC Act Section 5 unfairness doctrine shapes what “reasonable security” means in practice, enforced against companies with failed programs, not against a written standard. CMMC has contractual flow-down requirements that determine what your subcontractors must implement.
Reading these as legal documents, not just compliance matrices, changes which controls get prioritized and how the rationale gets documented.
The bigger structural shift isn’t tactical. It’s in how cross-functional conversations happen.
Legal and security typically run in parallel. Legal manages regulatory exposure; security manages technical risk. The interfaces between them, incident notification, vendor contracting, regulatory response, get handled reactively, under time pressure, by people who don’t fully understand the other side’s constraints.
Legal training doesn’t replace that interface. It makes the interface functional. When you can read a contract clause and identify the security implication, explain to outside counsel why forensic preservation needs to happen before the investigation concludes, or draft a notification letter that satisfies statutory requirements without over-disclosing, the program moves faster and makes fewer errors at the boundary between technical and legal risk.
Security professionals with legal training aren’t practicing law. The value is translation, working directly with counsel, understanding legal risk framing, and making technical decisions that account for it without needing every conversation mediated by subject matter experts on both sides.
Most organizations have a security program. Far fewer have one that accounts for the legal environment they operate in. Statutory language, contract interpretation, regulatory compliance, evidence rules, these aren’t separate from security work. They determine whether the security work holds up when it’s tested.
Hope you found this post helpful and informative. Thanks for stopping by!




Leave a comment